
Is your car spying on you? When safety and data privacy collide…
What sort of data collection is “fair and reasonable” when it’s your car doing the collecting?

‘Hi Scott, nice talking with you. We’ve got AV, some firewalls and spam filters for email…isn’t that enough? I think we are pretty secure”
This is probably the most consistent interaction I have with customers in the mid-market.
But what is ‘enough’ security?
It’s a question I get asked almost every day because it’s becoming increasingly difficult to answer. Part of that is due to the changing nature of the threats organizations face, but it’s also because our security mindset needs an upgrade. When it comes to “how much” cybersecurity organizations have, I see two buckets companies fall into most consistently.
The first bucket is where they’ve equipped themselves with some basic but necessary tools — a firewall, AV and malware protection, some data back-up, and a spam filter. I call this security hygiene. This is akin to a lock on the door of a house and making sure the house is organized so people aren’t hurting themselves by stepping on legos or bumping into furniture in the middle of the night. It’s making the space clean, easy to work in, and functional.
But unlike a house, where break-ins are relatively rare, organizations have to repel threat actors on a daily basis as adversaries don’t discriminate and businesses of any size are fair game. In your house, there are only so many access points that warrant security measures.
But in cybersecurity, even the tiniest gaps can be found and exploited. Depending on your organization’s attack surface, a hacker can make their way in via dozens, even hundreds of access points.
Which brings me into the second bucket I see other organizations fall into (and it’s the one I recommend), having a strong security posture.
Security posture is what organizations should be looking to build, and that means having more than just hygienic measures like a firewall or an AV in place. It’s about considering what’s necessary to stop an adversary before they can make their way across the entire kill chain. Without sounding too doom and gloom, in today’s world, you’re likely to be attacked. This isn’t paranoia talking, it’s just statistics. In 2020, the likelihood of a company suffering a data breach increased to 27.7%, or just a notch over 1 in 4.
With those odds, wouldn’t it make sense to prepare ahead of time?
Too many organizations fall into the first bucket and that’s partly because we just haven’t updated our security framework. Years ago, security hygiene was enough. Attack surfaces were smaller, compromises were less frequent and much less sophisticated. Hygiene made sense. Organizations, rightly so, focused on having a clean environment that had basic protections. But hygiene only gets you so far these days.
If you knew you had a more than 1 in 4 chance that your house would get broken into, what would you do? You’d make sure all methods of entrance are secure, you’ve got alerts in place that will tell you if someone’s broken in, and you’ve got mitigations in place that stop that burglar from stealing your most valued possessions.
As a simple example, a recent conversation with an organization that was breached brought in an incident response and recovery team. They asked to see the company’s logs so they could get more information about the attack. Unfortunately, the organization, unaware of how helpful it would be, didn’t keep logs. That made knowing how the breach happened and taking steps towards preventing another one, that much harder.
I tend to be a pragmatic and optimistic person, so I think it’s much less about fearing an attack, but being prepared for one.
When I speak to customers and other security leaders who think hygiene is enough, to be clear, they are not doing anything wrong, in fact everything they are doing is needed. It’s just not sufficient today.
To truly address the threats organizations face, leaders need to be thinking about the killchain and how they should build out their security priorities accordingly. I believe if we start thinking about the killchain as the driving force behind a company’s security posture, it will help businesses make clearer decisions, bring efficiencies to their security spending while reducing the pressure on their IT departments who are no doubt already under pressure.
A good starting point is using a cybersecurity framework such as the one that’s recommended by NIST. Here’s a quick breakdown of each of the functions within its framework:
Identify: Knowing how an attacker can get in requires you to understand your own organization and take stock of your assets, your environment, and third-party ecosystem. With existing processes, policies, and risk management strategies, you should have a strong sense of where your potential vulnerabilities lie while being able to map out your cybersecurity strategy moving forward.
This can be done with asset visibility and inventory tools, having a document risk management processes in place, and ensuring you’re part of conversations that affect your environment and potential vulnerabilities.
Protect: This is where security hygiene, for the most part, starts and stops. It’s pure defense and tries to keep the bad guys out. As mentioned, they will eventually find their way in so you can’t fully rely on protective services and tools.
Tools like spam filters and AVs keep a lot of the unsophisticated actors and attackers out but this is just a starting point. Locks on doors are good, but you also want to know who’s trying to get in. That’s where detect comes into play.
Detect: Who got in, through what manner, and which access point? This information is crucial in preventing another attack. We know bad guys are trying to get in but it’s also important to know who they are and what they’re doing. If a burglar got in through the back door, you might want to install a security camera in the backyard. If they picked your lock, you might want to invest in a better lock. The same principle applies here.
Investing in the right tools can let you know exactly when a malicious actor has reached your network or assets, giving you the needed time to react.
Here is where we adopt tools like an endpoint detection and response (EDR) solution alongside advanced email detection solutions that can detect business email compromise, advanced phishing and whaling attacks. The key here is to focus on lateral movement visibility so you not only detect whether someone entered your environment but you know where they’re headed.
You want to prioritize active directory visibility and managed services which will help tie in protective and detection services to best identify threats while providing the behavioral analytics that will tell you how your company was compromised. Once we have identified the attacker and the mode of attack, we can move onto the next step.
Respond: How quickly would you be able to protect your most sensitive assets if your network was breached? Do you have a response plan in place already? Your speed to response capability makes the difference in how affected your organization will be in the face of a compromise.
This is why, especially for mid-market companies, we encourage leveraging MSSPs and the right technology to make your response much faster and accessible to a crew of experts that your organization may not necessarily have in-house.
Recover: Unprepared organizations can be crippled by the smallest cyber attack. Your priority should be to have the tools necessary to get back to BAU (business as usual) as fast as possible. Having a strong response plan in place will naturally guide your ability to recover.
This includes having a communication plan in place for internal and external purposes, having a mitigation plan in place for common scenarios. This could mean having backups in place in case of a ransomware attack or leveraging detection and response tools to isolate attackers and affected environments so your entire network or infrastructure isn’t hampered.
Adopting a new framework, thinking through a compromise scenario, and considering the killchain when assessing potential threats should empower you, so you can prepare your organization for any kind of attack. It’ll also help you identify any blind spots in your current environment so you’ll know where to prioritize future efforts. One thing I will say here, a lot of the above may sound daunting, but with the right partner, it can be a pretty straightforward and painless exercise to get these components in place.
Cybersecurity leaders have a tough job. They need to constantly be up to date with the latest threats while trying to secure an ever-changing organization. Between resources that never seem like they’re enough and overstated promises that lead to less-than-stellar purchases, leaders have enough to deal with internally before even thinking about the numerous external threats waiting to compromise their organization.
Given how crowded the security industry is, we believe it’s part of our job to bridge that knowledge and experience gap, and try and facilitate a strong security posture in an easy and accessible manner. We want to help them understand how far their current configuration gets them, and how much further they can get with us. It can be a challenging conversation — leaders may not agree that the technology they decided to purchase a few years ago isn’t enough, or they may think we’re judging their professional capabilities.
We’re not. We’re just trying to help everyone move forward so they are protected, confident and able to get about their business without having to worry or deal with a significant event. If this article is helpful or you have questions, please feel free to reach out! Always happy to discuss.

What sort of data collection is “fair and reasonable” when it’s your car doing the collecting?

SMEs have little wiggle room regarding cybersecurity. Smaller budgets and fewer dedicated security resources mean that cyberattack attempts are more likely to penetrate an SME’s defenses than those of a larger company. Forty-three percent of all cyberattacks are aimed directly at small to medium businesses, and only 14% of SMEs are ready to defend against those attacks, according to a study by Accenture. Aside from being extremely inconvenient, these data breaches also get expensive. The cost of data breaches to […]
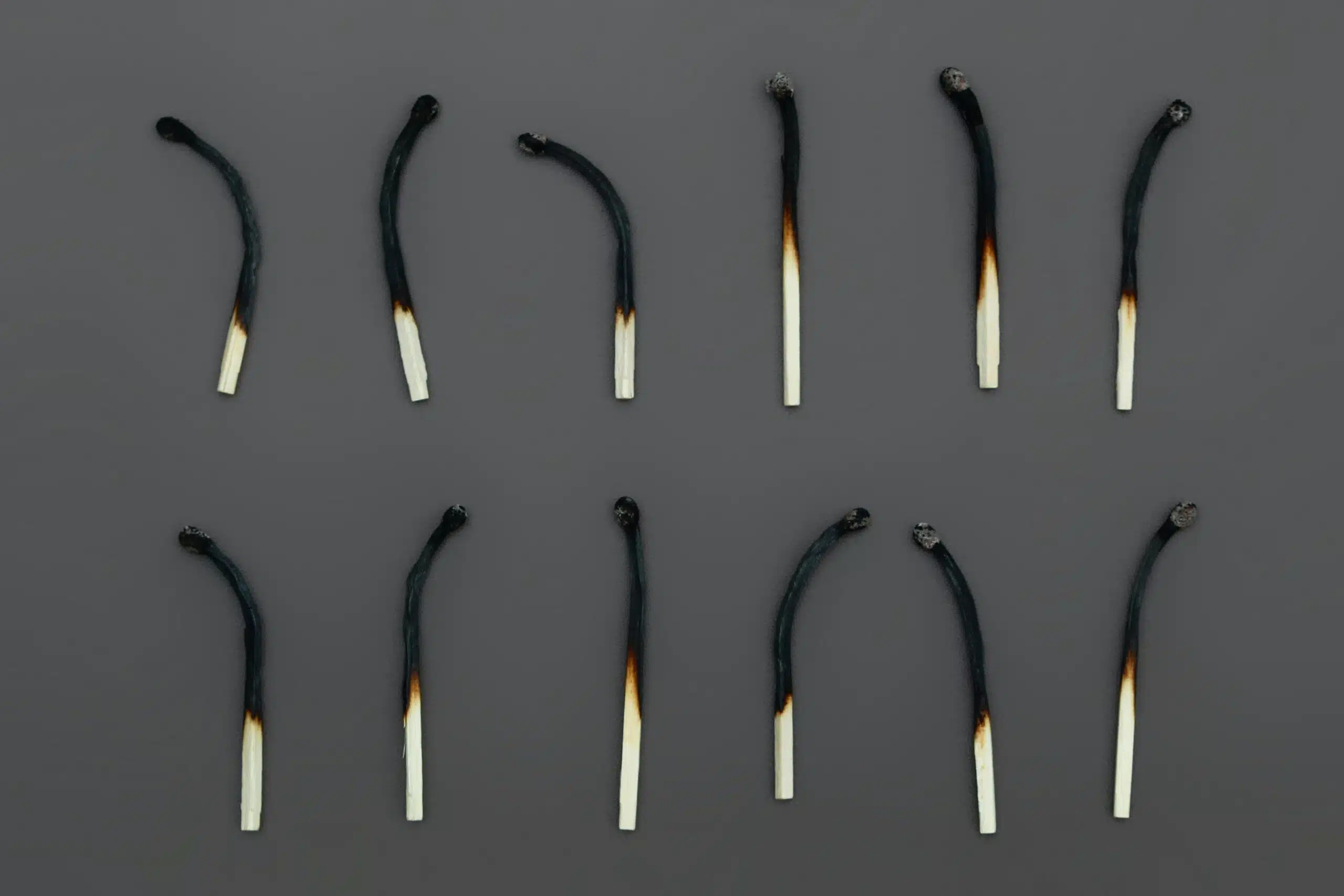
Burnout Math Doesn’t Work Anymore


By subscribing you agree to our Privacy Policy and provide consent to receive updates from our company.






