
BitLocker in crisis? The “YellowKey” zero-day in plain English
Nightmare Eclipse hates Microsoft, loves dropping 0-days.
By subscribing you agree to our Privacy Policy and provide consent to receive updates from our company.
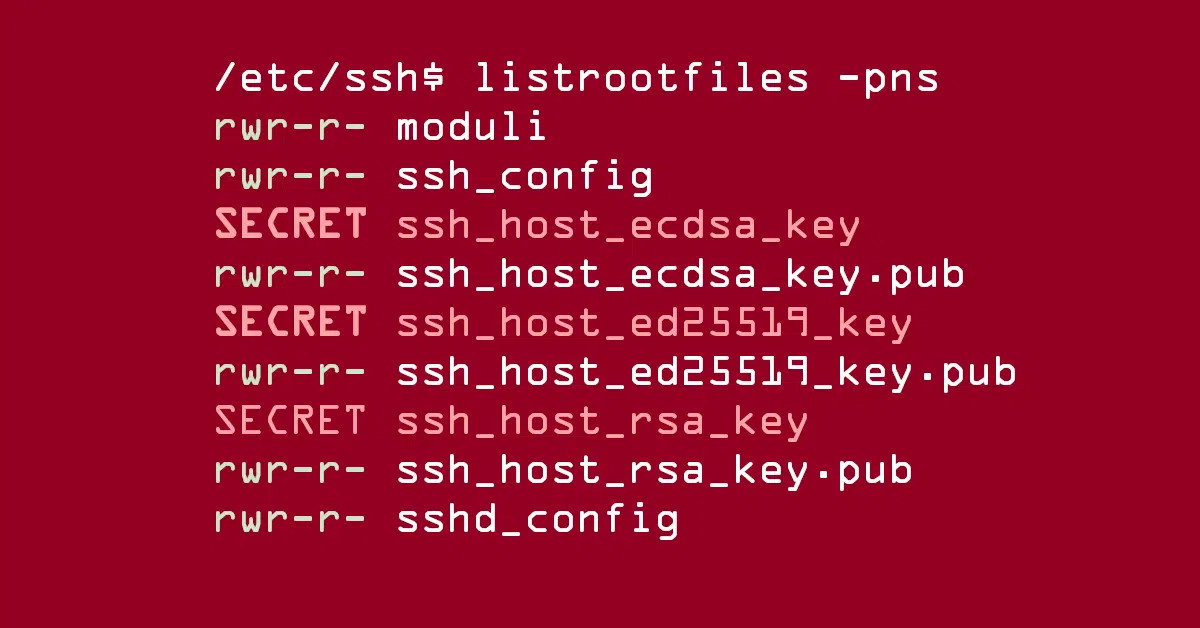
Exploits target SSH keys and system password hashes

Security budgets aren’t increasing, but security pressures are.


Not to say, “We told you so,” but Linux has two more bugs-with-logos already.

Seen posts implying Let’s Encrypt got hacked? They were wrong!

The Copy Fail bug has attracted lots of copy-and-paste publicity lately. We tease the facts from the fiction.

Cold War cryptographic capers in a real-world Spy vs. Spy scenario!

Non-human identities such as API keys, OAuth tokens, AI agents, and service accounts, now surpass human identities by 144 to 1.
Full disclosure carnival turns ‘Defender’ into ‘Attacker.’
Burnout Math Doesn’t Work Anymore
There’s an intriguing “post-quantum” bugfix in the latest OpenSSL release
Tragic death of “invisible” cyclist in road-race crash – would live tracking have helped?


The ‘TeamPCP’ cybergang is all over the media – here’s why, and what to do

Strong words from Duck and David! (But with humor and good grace throughout.)

Popular cybersecurity scanning tool turns into info-stealing malware
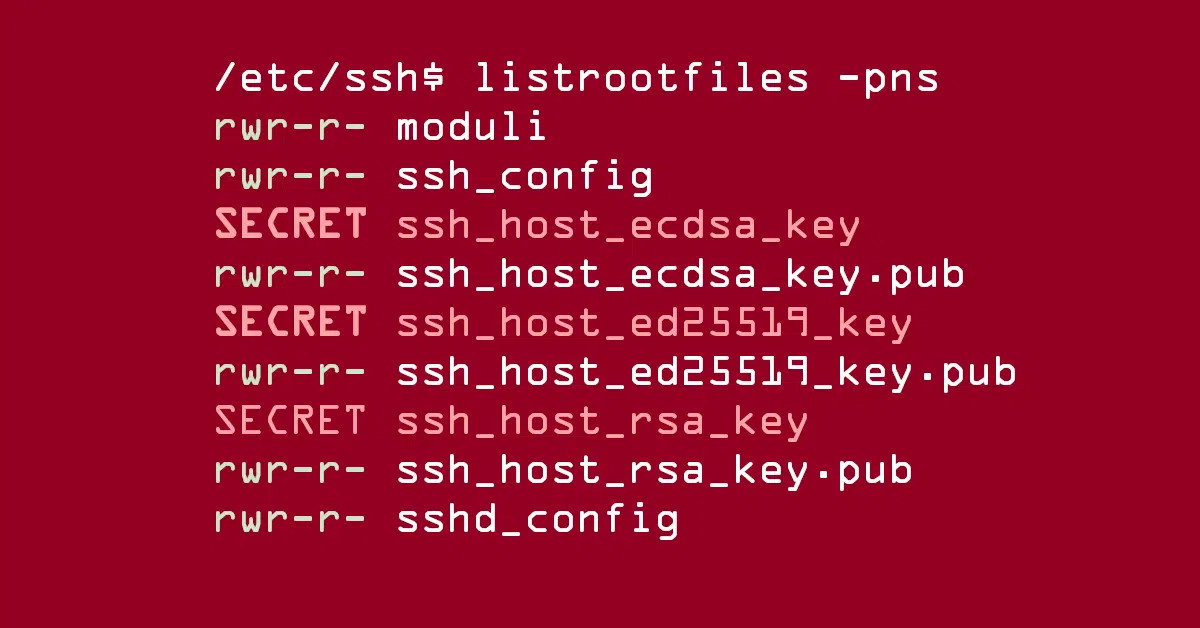
Exploits target SSH keys and system password hashes

Security budgets aren’t increasing, but security pressures are.

Not to say, “We told you so,” but Linux has two more bugs-with-logos already.
By subscribing you agree to our Privacy Policy and provide consent to receive updates from our company.

Seen posts implying Let’s Encrypt got hacked? They were wrong!

The Copy Fail bug has attracted lots of copy-and-paste publicity lately. We tease the facts from the fiction.

Cold War cryptographic capers in a real-world Spy vs. Spy scenario!


Non-human identities such as API keys, OAuth tokens, AI agents, and service accounts, now surpass human identities by 144 to 1.



Tragic death of “invisible” cyclist in road-race crash – would live tracking have helped?

The ‘TeamPCP’ cybergang is all over the media – here’s why, and what to do

Strong words from Duck and David! (But with humor and good grace throughout.)

Popular cybersecurity scanning tool turns into info-stealing malware



By subscribing you agree to our Privacy Policy and provide consent to receive updates from our company.






