When anti-virus goes rogue – A trifecta of Defender zero-days
Full disclosure carnival turns ‘Defender’ into ‘Attacker.’
Full disclosure carnival turns ‘Defender’ into ‘Attacker.’
Burnout Math Doesn’t Work Anymore

Duck and David have a spirited but not irreverent discussion about metrics and measurement. Well, not too irreverent…

It’s binding for federal agencies, but worth your attention even if you’re not bound by it yourself.
Citrix patched its NetScaler products two months ago, but CERTs are still begging companies to update…

Join Duck and David as they talk about outsourcing, SOC response, and cybersecurity dialog. (The human sort!)

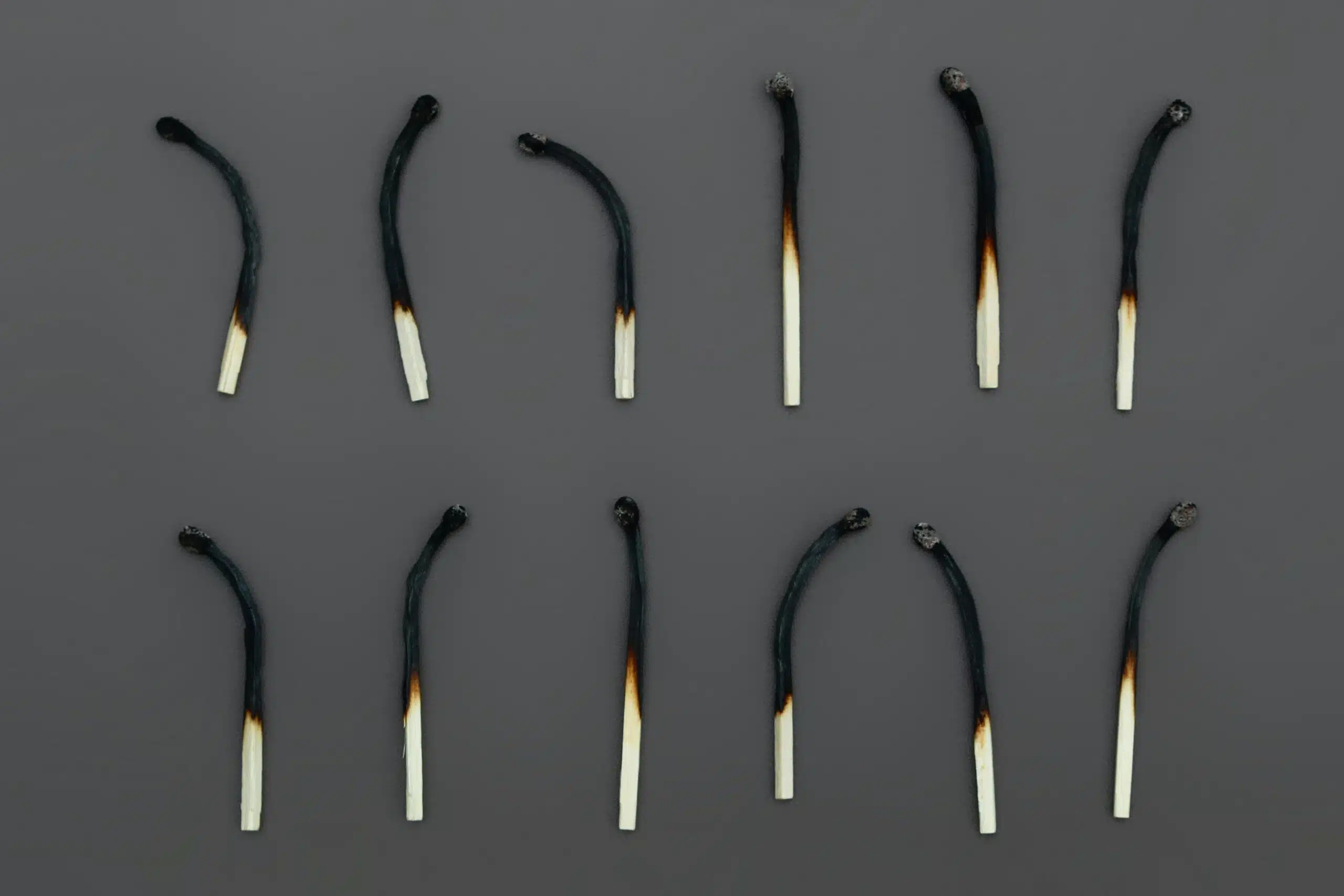
July’s Patch Tuesday was supposed to fix these holes. Sadly, attackers have worked out that the patches weren’t sufficient…

Organizational risk is no longer limited to the office. It has spread to the cloud, third parties, and employee devices. We discuss why mobile device security needs to be made a priority.

New HIPAA regulations now demand adherence. Find out what’s required.

As the cybersecurity vendor market matures, it’s hard to know what’s best for your organization.

We know what you’re thinking. Should the word “beachhead” be “breachhead”?

Seasonal fun – with a gently serious side.

Organizations are becoming more aware of the need for MDR (managed detection and response) services to achieve real cyber resiliency. The increase in the quantity and sophistication of cyberattacks means that other, siloed solutions, fall short of fully protecting your organization. Whereas no one can guarantee that you won’t fall victim to a cyberattack, the use of MDR significantly decreases that risk and its overall impact. Implementing MDR also gives you the greatest chance of effectively and rapidly recovering from […]

As cyber threats became more evolved and sophisticated, the cybersecurity industry responded by developing more complex technologies. These technologies included the ability to detect intrusions through behavioral analysis, as well as advanced technologies for determining patterns from numerous data sources that indicate a compromise or that an unauthorized user is lurking in an organization’s network. Each advancement improved the ability of cybersecurity professionals to combat cyber threats, but it also started siloing cybersecurity solutions. Eventually, multiple technologies and tools existed […]

By subscribing you agree to our Privacy Policy and provide consent to receive updates from our company.






