Tales from the SOC: Classic Crypto – Operation GUNMAN | S1 Ep023
Cold War cryptographic capers in a real-world Spy vs. Spy scenario!
By subscribing you agree to our Privacy Policy and provide consent to receive updates from our company.
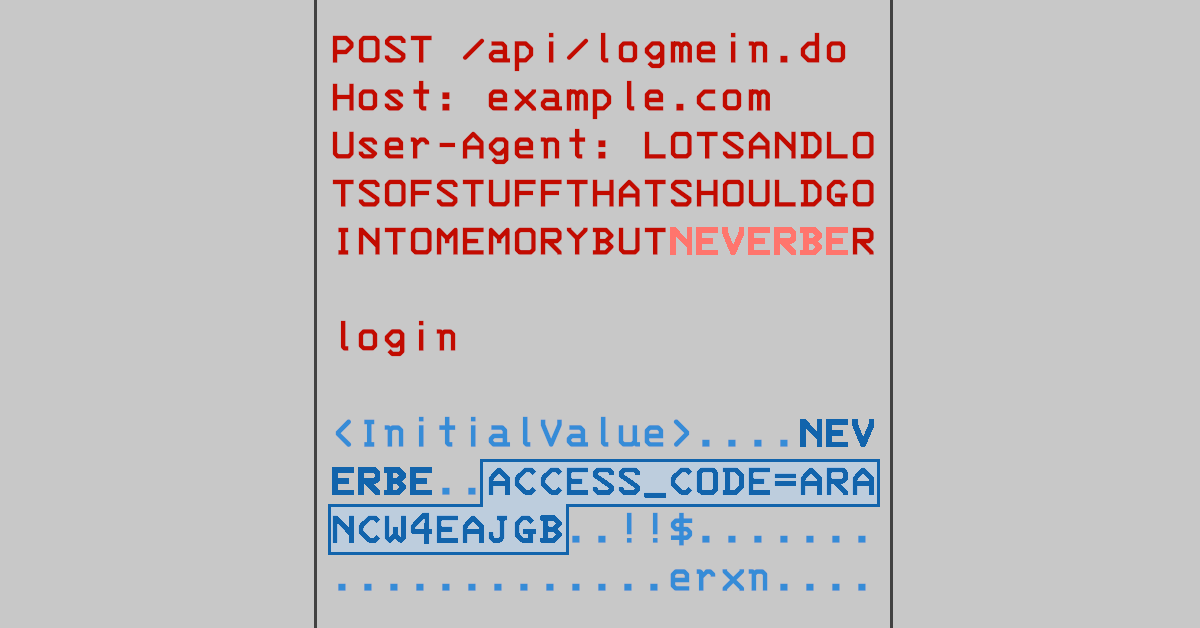
Citrix patched its NetScaler products two months ago, but CERTs are still begging companies to update…

While agentic AI is powerful, it is not a silver bullet.


Just how safe are public power outlets and borrowed chargers?

Learn how to successfully train your employees on cybersecurity threats.
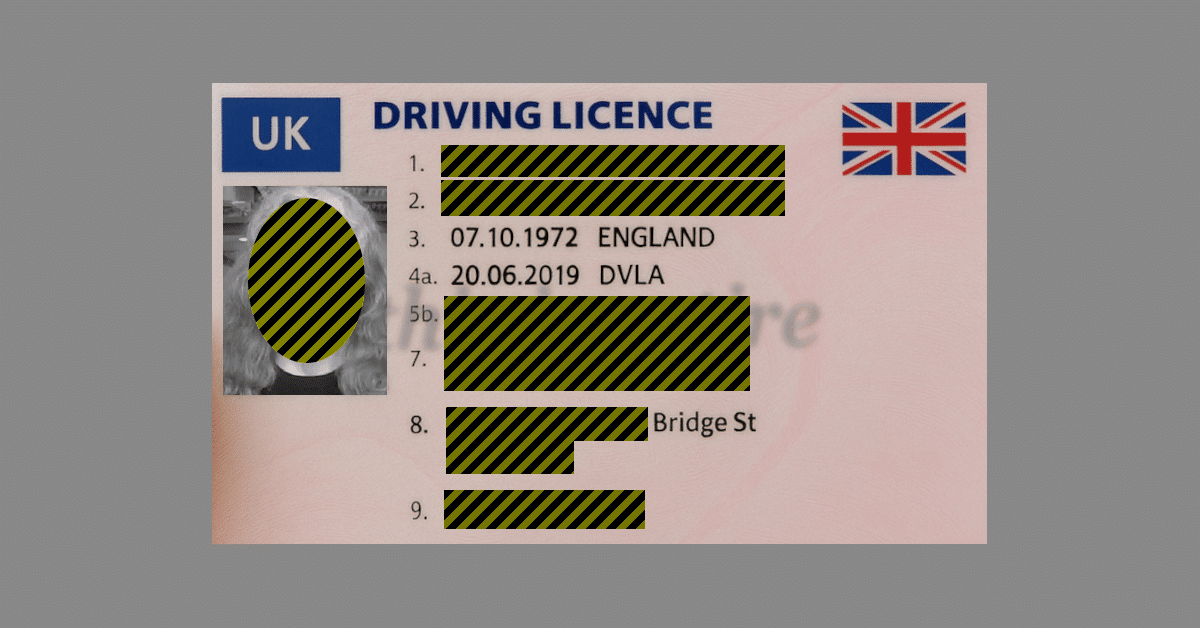
Fake IDs say “this is satire” in the background, but please don’t try to use one, even as a joke!

Join Duck and David as they talk about outsourcing, SOC response, and cybersecurity dialog. (The human sort!)

Learn about the top three challenges companies face with MDM implementations.

July’s Patch Tuesday was supposed to fix these holes. Sadly, attackers have worked out that the patches weren’t sufficient…
Public-key cryptography is useful for secure logons. Just make sure you know the table stakes before joining the game…
Chinese cybercrime suspect takes vacation to Italy. Now faces a much, much longer side-trip to the US.

As the Roman satirist Juvenal asked nearly 2000 years ago, “Who will guard the guards themselves?”


Understand why traditional MDM has its drawbacks when it comes to security.

Will we ever conquer the scourge of ransomware? Can rules and regulations help?

Remember Stingrays? Turns out that rogue phone base stations can be used for blasting scams TO you, as well as snooping on messages FROM you.
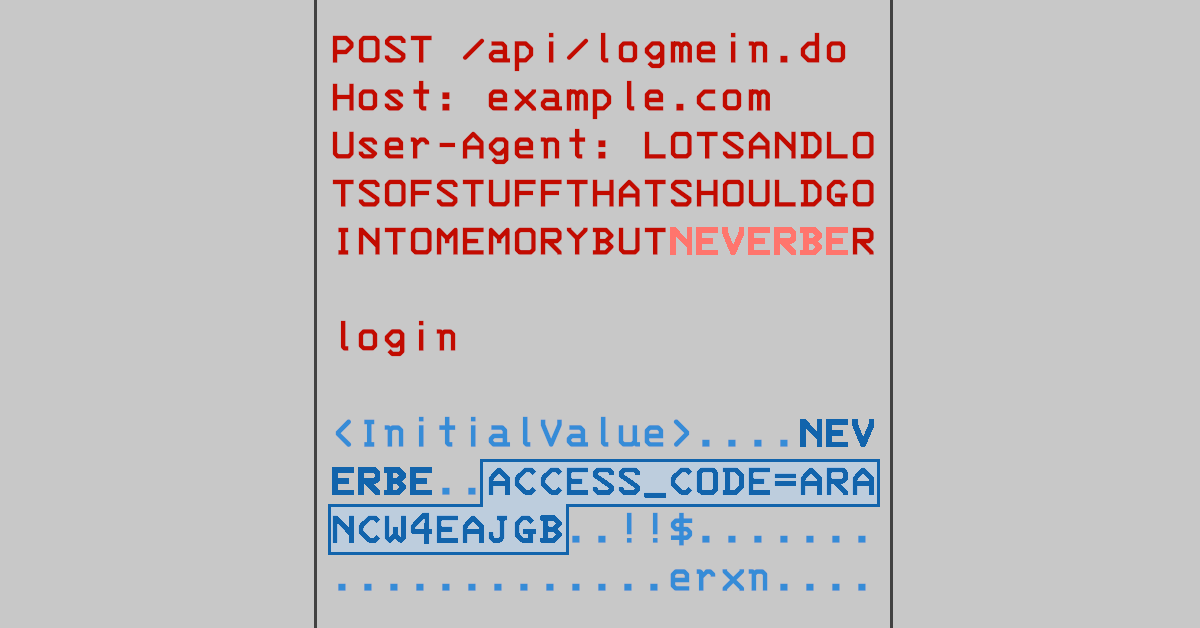
Citrix patched its NetScaler products two months ago, but CERTs are still begging companies to update…

While agentic AI is powerful, it is not a silver bullet.

Just how safe are public power outlets and borrowed chargers?
By subscribing you agree to our Privacy Policy and provide consent to receive updates from our company.

Learn how to successfully train your employees on cybersecurity threats.
Fake IDs say “this is satire” in the background, but please don’t try to use one, even as a joke!

Join Duck and David as they talk about outsourcing, SOC response, and cybersecurity dialog. (The human sort!)


Learn about the top three challenges companies face with MDM implementations.



As the Roman satirist Juvenal asked nearly 2000 years ago, “Who will guard the guards themselves?”

Understand why traditional MDM has its drawbacks when it comes to security.

Will we ever conquer the scourge of ransomware? Can rules and regulations help?

Remember Stingrays? Turns out that rogue phone base stations can be used for blasting scams TO you, as well as snooping on messages FROM you.



By subscribing you agree to our Privacy Policy and provide consent to receive updates from our company.