News in Brief: Suspects in kindergarten cyber-blackmail case arrested in UK
Allegedly published childrens’ photos and family data, and even called up parents to push for payment.
Allegedly published childrens’ photos and family data, and even called up parents to push for payment.

Your Smart TV is a server that sits alongside your work laptop and the rest of your home network…

How to stay secure in an AI attackers’ world. It’s not as scary as some people seem to think!
AI is woven into to this cyberattack in several fascinating ways.
Agentic AI is transforming cybersecurity, but it’s not a substitute for human expertise. Here’s why.

Insider threats often involve bribery, corruption, and cold hard cash. But not always…
Learn about AD attacks and how hackers are getting access into your network.

Writing non-Play Store apps? You’ll have to show ID and pay a fee anyway.

What if your attackers don’t need any technical skills? What if you let them in yourself, simply by being too helpful?

Here’s how ID-based attacks can impact companies.
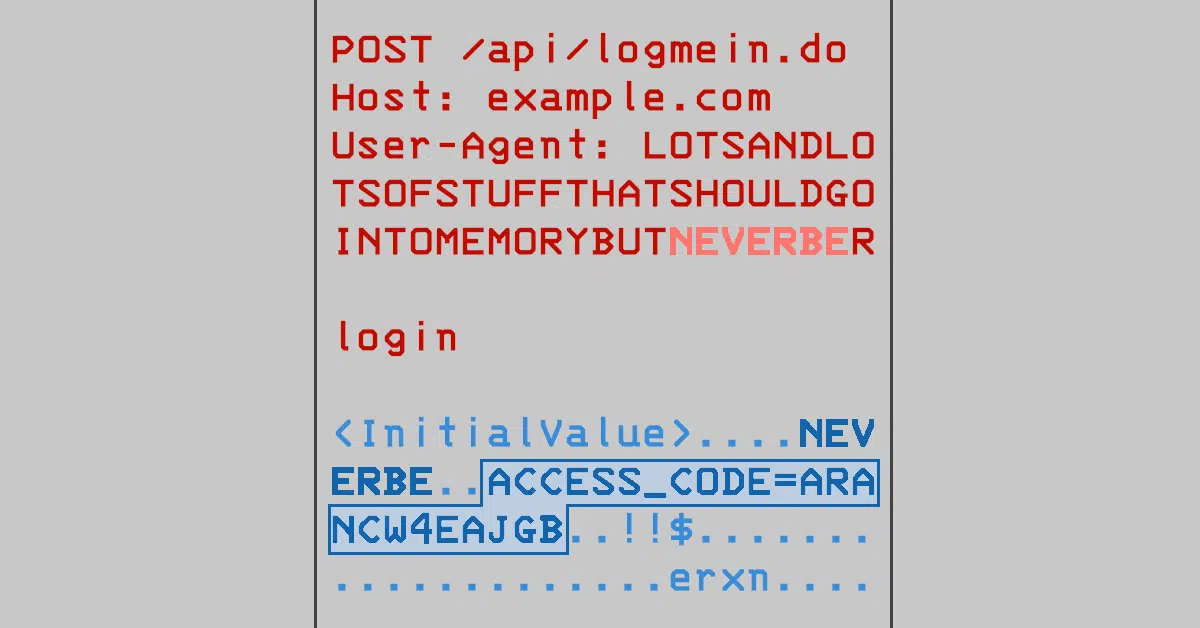
Citrix patched its NetScaler products two months ago, but CERTs are still begging companies to update…

Just how safe are public power outlets and borrowed chargers?

Join Duck and David as they talk about outsourcing, SOC response, and cybersecurity dialog. (The human sort!)

July’s Patch Tuesday was supposed to fix these holes. Sadly, attackers have worked out that the patches weren’t sufficient…

By subscribing you agree to our Privacy Policy and provide consent to receive updates from our company.






