There’s a conversation happening quietly in CISO offices right now — not about zero-days or ransomware gangs, but about people. Specifically, about the growing gap between the security team that exists on the org chart and the one the business actually needs to stay protected.
The cybersecurity talent shortage isn’t new. We’ve been talking about it for a decade. But the shape of the problem has fundamentally changed, and many security leaders are still trying to solve a 2018 talent problem with a 2018 playbook.
The Burnout Math Doesn’t Work Anymore
Let’s be direct about what’s happening on most security teams right now.
Analysts are drowning in alerts they know are mostly noise but can’t ignore because one real threat might be hiding somewhere inside the flood. According to research by Osterman, almost 90% of SOCs are overwhelmed by backlogs and false positives, and 80% of analysts report feeling consistently behind in their work. Engineers are being asked to learn AI security, cloud-native architecture, and identity governance simultaneously, while also keeping the lights on for legacy infrastructure that nobody has budget to retire. Senior practitioners are fielding calls from recruiters every other week; and, increasingly, they’re picking up.
The numbers reflect the strain. According to Proofpoint’s 2025 Voice of the CISO report, 63% of CISOs experienced or witnessed burnout in the past year, with Sophos putting that figure even higher at 76%. Sophos also found that the problem is accelerating — 69% of respondents said burnout increased from 2023 to 2024 alone.
Meanwhile, the threat landscape hasn’t paused to let anyone catch their breath. AI is making phishing more convincing, attack surfaces are expanding faster than headcount can scale, and the regulatory environment means every incident carries more reputational and legal weight than it did before.
The old response — hire more people, buy more tools — is no longer viable for most organisations. Budget is compressed. The talent pool is shallow. And adding more tools often just creates more alert noise, which is the problem you were trying to solve in the first place.
A Shortage That No Hiring Plan Can Fix
The scale of the global talent deficit is staggering. According to ISC2’s 2024 Cybersecurity Workforce Study, the global cybersecurity workforce gap now stands at 4.8 million unfilled roles — a 19% increase year-over-year. The total workforce would need to nearly double just to meet current demand.
Filling individual vacancies is no easier. Nearly half of all organisations take more than six months to fill a cybersecurity role, and a BCG and Global Cybersecurity Forum report notes that the 28% vacancy rate in cybersecurity is actively impairing organisations’ ability to respond to escalating threats.
What’s changed in 2025 is arguably the most telling detail of all. For the first time, “lack of budget” has overtaken “lack of available talent” as the top reason organisations can’t fill security roles, according to the ISC2 study. The hiring crisis has evolved from a pipeline problem into a direct reflection of financial constraints — and that means the traditional fix of simply spending more on recruitment is no longer on the table for most teams.
The Org Design Rethink That’s Actually Happening
Smart security leaders aren’t just trying to hire their way out of this. They’re rethinking the structure of their teams from the ground up. A few patterns are emerging consistently.
- Eliminating L1 as a career path. The traditional tiered SOC model — L1 triages, escalates to L2, L2 escalates to L3 — made sense when threats were slower and more predictable. Today, it forces talented analysts to spend the majority of their time on work that is repetitive, low-judgment, and deeply demoralising. The SANS 2024 SOC Survey found that 70% of SOC analysts with five years of experience or less leave their role within three years — a damning indictment of the Tier 1 model. Organisations that are retaining analysts are the ones using automation and AI tooling to eliminate the soul-crushing work at the bottom of the funnel, so that human analysts are spending their time on work that actually requires human judgment.
- Embedding security into product and engineering. The perimeter is gone. The idea that a centralised security team can monitor and protect every system from a single command centre is increasingly a fiction. Security leaders who are winning are distributing security expertise — embedding security engineers directly into product squads, establishing “security champions” programs in development teams, and shifting left so that security is baked into build processes rather than bolted on at the end.
- Redesigning roles around outcomes, not functions. Many security job descriptions are artifacts of an older era — rigid functional roles that look great on an org chart but create silos that slow down response. The move is toward smaller, more cross-functional teams with clear ownership over security outcomes: protect this asset class, own incident response for this business unit, reduce risk in this part of the supply chain. Accountability becomes clearer, which also makes career growth easier to articulate.
- Building retention around career architecture. Compensation matters, but it’s rarely why good people leave. They leave because they can’t see a path forward, because they feel like they’re fighting the same battles with no progress, or because the work stopped being interesting. ISC2’s data shows that cybersecurity job satisfaction dropped to 66% in 2024 — a four-point decline in a single year. Investing in structured career progression, visible promotion criteria, and access to emerging skill areas — AI security, cloud-native defence, threat intelligence — is what differentiates teams that retain talent from those in permanent recovery mode.
The Dangerous Assumption Underneath All of This
Here’s the uncomfortable truth that isn’t said often enough: many security teams are operating with a silent, unacknowledged dependency on a handful of key people — usually two or three individuals who carry disproportionate institutional knowledge, work disproportionate hours, and hold the whole system together through sheer individual effort.
This is not a talent strategy. It’s a single point of failure wearing a badge.
When those people burn out, get poached, or simply decide they’ve had enough, the organisational impact is severe and immediate. It’s not just the headcount loss — it’s the loss of the mental model of how your environment works, the relationships with the business units, the unwritten knowledge of what “normal” looks like on your network, so you can recognise when something isn’t.
The data on CISO-level turnover alone should give boards pause. According to Cybersecurity Ventures, average CISO tenure sits at just 18 to 26 months — less than half the C-suite average of 4.9 years. Gartner has estimated that nearly half of cybersecurity leaders will change roles in a given period, with 25% citing work-related stress as the primary driver. And Devo Technology research found that 83% of IT security professionals believe burnout has directly caused data breaches at their organisations, while 77% say their stress levels directly affect their ability to keep customer data safe.
The org redesigns described above help. But they don’t fully solve the problem of structural fragility in a security organisation operating with lean headcount in a high-demand market.
A Structural Solution Worth Serious Consideration
Increasingly, forward-thinking security leaders are arriving at the same conclusion: trying to build and maintain a fully self-sufficient internal security function — one that covers detection, response, threat intelligence, vulnerability management, and beyond — is a bet that the talent market simply won’t let most organisations win consistently.
This is where a genuinely skilled, human-led Managed Security Service Provider (MSSP) changes the equation entirely.
Not all MSSPs are created equal. The legacy version of this model — a monitoring service that floods you with alerts and leaves the actual work to your already-stretched team — doesn’t solve the problem, it just moves it around. What’s changed is the emergence of truly modern, human-led managed security operations that combine expert practitioners with the right tooling and take full ownership of detection, response, and remediation.
SolCyber is purpose-built for exactly this challenge. As a fully managed, human-led MSSP, SolCyber puts the ‘Managed’ and ‘Response’ back into MDR — combining experienced practitioners with a curated, enterprise-grade security stack that covers endpoint, identity, email, and cloud environments. Rather than adding to alert noise or shifting burden back onto internal teams, SolCyber absorbs that operational weight entirely, operating as a true extension of your security function with full transparency and no black boxes.
For security leaders navigating talent fatigue, this model offers something the traditional hiring market cannot: resilience that isn’t dependent on any single person, consistent expertise that scales with your environment, and the ability to redirect your internal team’s energy toward strategic work — business alignment, architecture, governance, and the things that require deep organisational context that only an insider can provide.
The security organisation of the future probably isn’t a larger version of the one you have today. It’s a leaner, higher-leverage, internal team working in close partnership with external experts who handle the operational depth that no reasonable hiring plan can sustainably staff.
That’s not a compromise. For most organisations, it’s the smartest structural decision a security leader can make.
Interested in what a human-led managed security model looks like in practice? Learn more about SolCyber’s approach to managed security services.
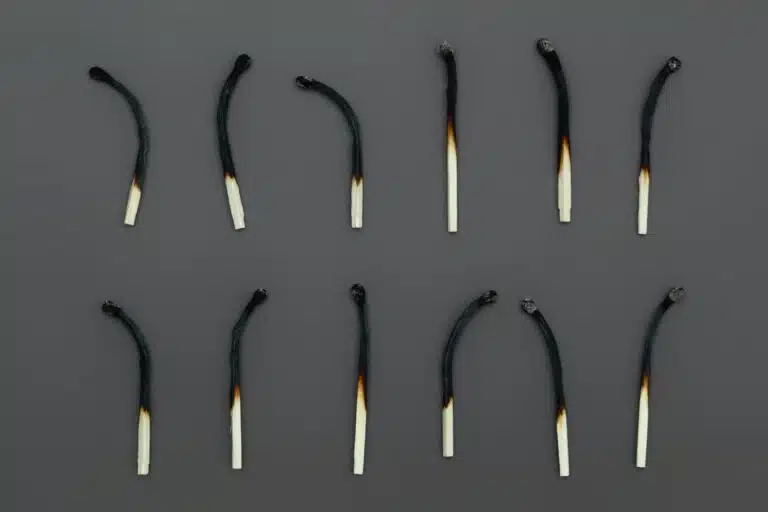
Photo by Anne Nygård on Unsplash