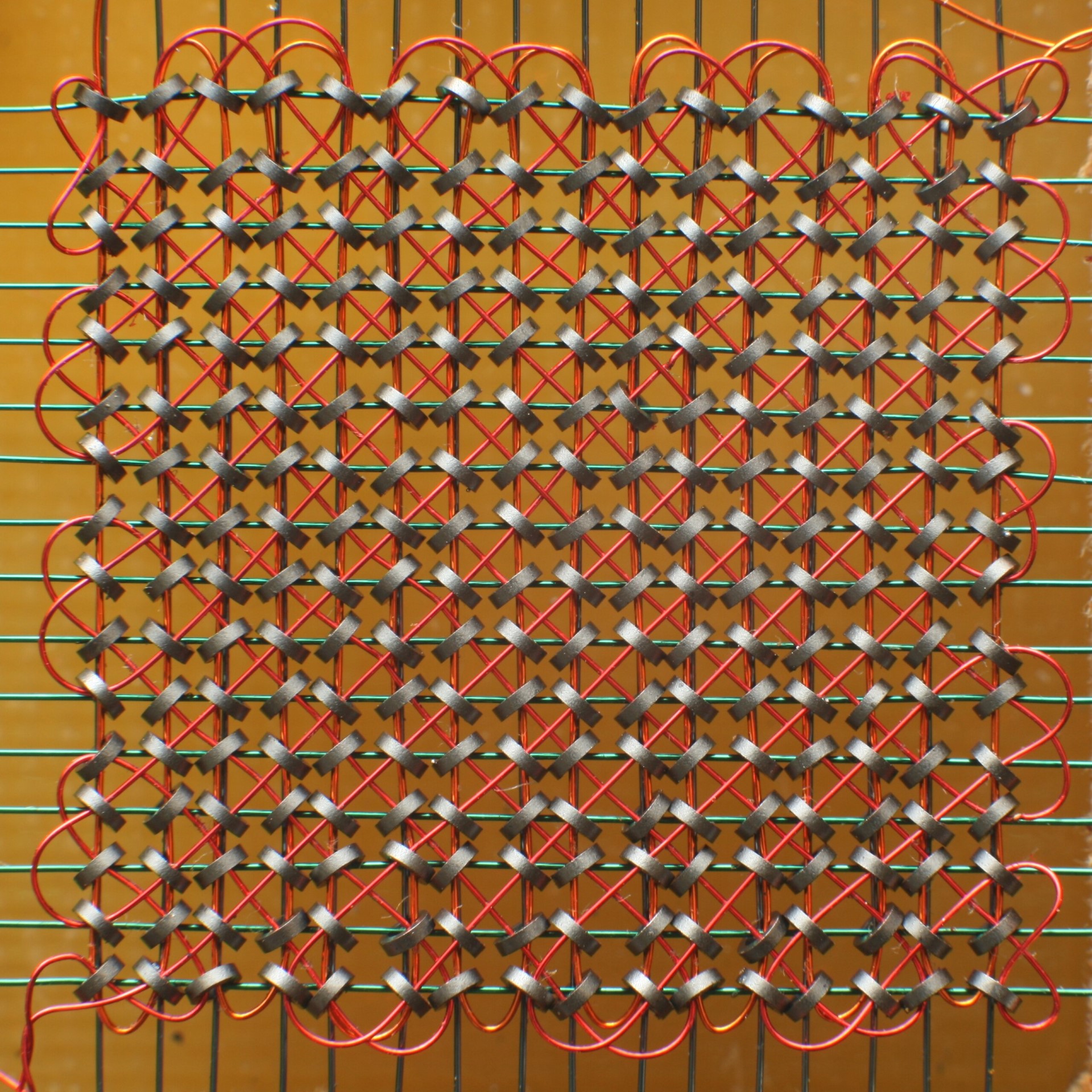
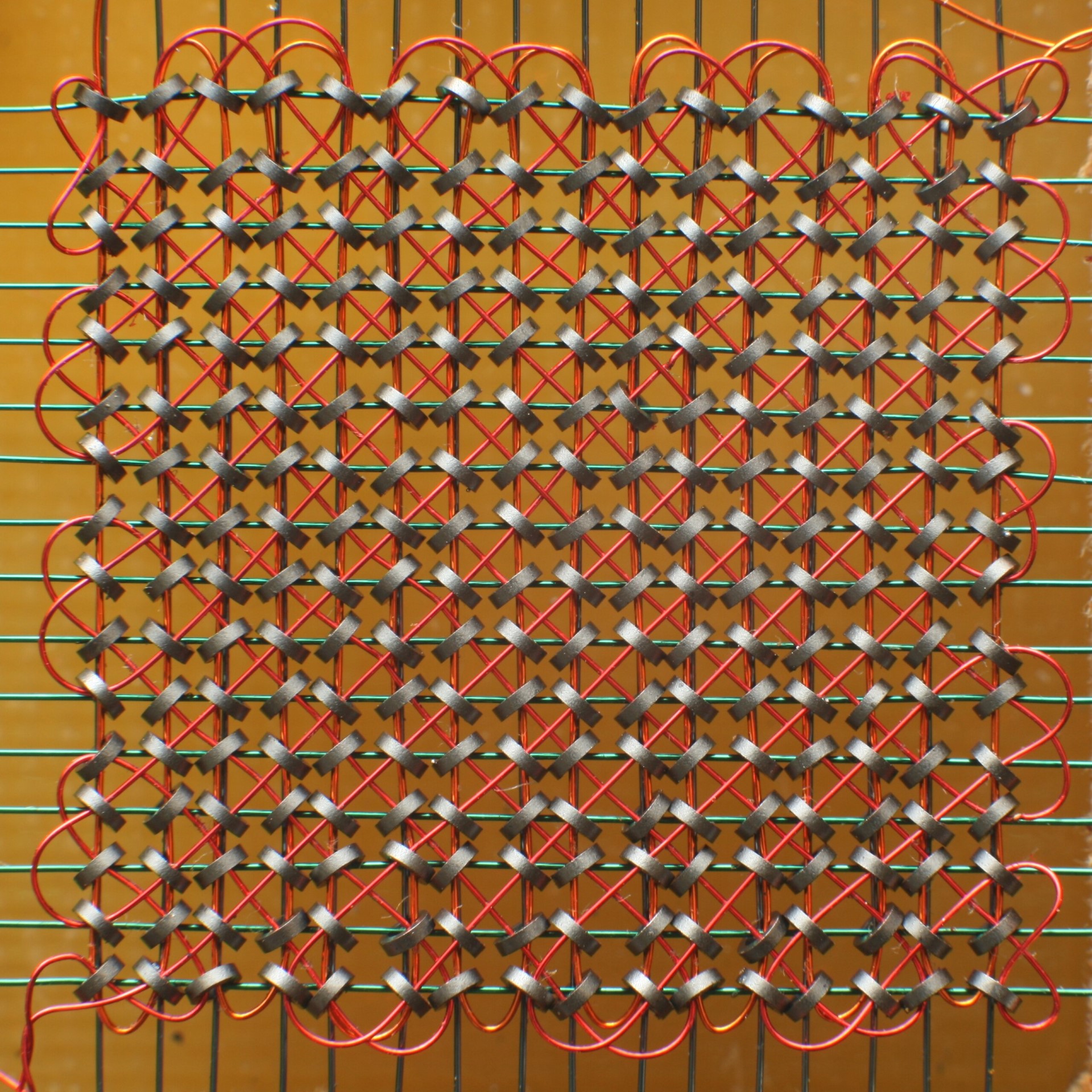
Tales from the SOC: Classic Crypto – Operation GUNMAN | S1 Ep023
Cold War cryptographic capers in a real-world Spy vs. Spy scenario!
By subscribing you agree to our Privacy Policy and provide consent to receive updates from our company.

Strategies for Safe and Private Communication for Organizations Malware and phishing scams aren’t the only cybersecurity risks that emails pose. The content of the emails themselves can be its own risk factor. Email content can include a treasure trove of exploitable information for cybercriminals. Employees may send passwords or social security numbers via email or share sensitive company information with no way of retracting the email once it’s sent. John Podesta, Hillary Clinton’s campaign manager in 2016, had his Apple […]

So many breaches! Such dramatic graphs! So much malware! Such huge numbers!


As the tech landscape becomes increasingly vast yet more interconnected and bad actors utilize more advanced techniques, the process of building a security strategy and implementing that strategy is becoming ever more complex. Although new point solutions and service offerings are emerging to address some of those complexities, it doesn’t do much to help businesses that don’t have the expertise, time, or budget to operationalize a whole security tech stack. This speaks to the larger problem of operationalizing cybersecurity. As […]
Malware writeups used to tell you everything there was to know about each new threat. But life’s not like that today, and it’s not because threat researchers aren’t as smart or as diligent as they used to be!

Phishing remains one of the most prominent attack vectors in use today. According to the Cybersecurity and Infrastructure Security Agency (CISA), over 90% of all cyber attacks begin with phishing. Two core reasons for phishing’s prominence are: By the end of Q4 2022, the number of phishing attacks worldwide spiked to over 1.35 million. Phishing is often the first step in far more sophisticated attacks, such as: Investing in fortifying your business against phishing attacks is one of the more […]

Our newest writer, Paul Ducklin, tells it as he sees it – that we’re all served better when we treat cybersecurity as a value to be maximised, not as a cost to be minimised.

Cybersecurity is constantly evolving. As technology changes, new threats emerge, and companies are forced to find new ways to defend their organizations against those threats. Every so often, however, changes build to the point that the old way of doing things no longer works and a seismic shift is necessary. The cybersecurity industry is currently at this inflection point where something has to change. Breaches are on the rise and attackers are increasingly successful in their efforts. Cybersecurity is becoming […]

Our latest addition to the content team at SolCyber is none other than trusted cybersecurity authority Paul Ducklin, so we asked him to introduce himself in no uncertain terms!

Enterprises are attractive, high-value targets for hackers; and, because enterprises often have more employees and a more complicated environment, protecting against phishing and social engineering attacks is even more difficult. The Dropbox breach of late 2022 is a prime example of this weakness. Hackers emailed a large number of Dropbox employees, directing them to a malicious website where their credentials were stolen. This kind of risk is more common than not. According to the 2023 Verizon Data Breach Report, 74% […]

Email is the second-most common vector for cyberattacks, according to the latest data breach report from Verizon while IBM’s Cost of a Data Breach report for 2023 indicates that Business Email Compromise (BEC) attacks, one type of email attack, resulted in an average loss of $4.67 million. Clearly, these attacks are succeeding against organizations. However, by following a few best practices, you can prevent many of the most common email-based cybersecurity incidents. 1. Invest in email/spam filters A sophisticated email […]

2023 has furnished an onslaught of data breaches, smashing 2022’s numbers, and putting an exclamation point on the need for companies of every size to invest in cybersecurity. By September 2023, there were already 20% more data breaches in the US than in the entirety of 2022. Probably most alarming is that 98% of all organizations have a relationship with at least one vendor that has been breached in the last two years. In an extensive study of the 2023 […]


Phishing emails are often sent out en masse and target people indiscriminately. According to a recent Gone Phishing Report, 7% of users clicked a phishing email in 2022. Of those, 44% submitted credentials in a subsequent online form. As high as these statistics are, spear phishing attacks–a highly targeted form of phishing–are much more successful. According to research by Barracuda, 11% of spear phishing email recipients click the links inside them. Let’s dive into what spear phishing is, why it’s […]

Enterprises are attractive, high-value targets for hackers; and because enterprises often have more employees and a more complicated environment, protecting against phishing and social engineering attacks is even more difficult. The Dropbox breach of late 2022 is a prime example of this weakness. Hackers emailed a large number of Dropbox employees, directing them to a malicious website where their credentials were stolen. This kind of risk is more common than not. According to the 2023 Verizon Data Breach Report, 74% […]

Business Email Compromise (BEC) is a type of email cybercrime in which attackers impersonate the owner of an email account in an effort to defraud a company. The attack, which is increasing in prevalence, often looks to obtain funds or credentials. Global losses from BEC attacks have increased by 17% from December 2021 to December 2022, reports the FBI’s Internet Crime Complaint Center (IC3). From October 2013 to December 2022, the IC3 recorded over $50 billion in global losses due […]

Strategies for Safe and Private Communication for Organizations Malware and phishing scams aren’t the only cybersecurity risks that emails pose. The content of the emails themselves can be its own risk factor. Email content can include a treasure trove of exploitable information for cybercriminals. Employees may send passwords or social security numbers via email or share sensitive company information with no way of retracting the email once it’s sent. John Podesta, Hillary Clinton’s campaign manager in 2016, had his Apple […]

So many breaches! Such dramatic graphs! So much malware! Such huge numbers!

As the tech landscape becomes increasingly vast yet more interconnected and bad actors utilize more advanced techniques, the process of building a security strategy and implementing that strategy is becoming ever more complex. Although new point solutions and service offerings are emerging to address some of those complexities, it doesn’t do much to help businesses that don’t have the expertise, time, or budget to operationalize a whole security tech stack. This speaks to the larger problem of operationalizing cybersecurity. As […]
By subscribing you agree to our Privacy Policy and provide consent to receive updates from our company.
Malware writeups used to tell you everything there was to know about each new threat. But life’s not like that today, and it’s not because threat researchers aren’t as smart or as diligent as they used to be!

Phishing remains one of the most prominent attack vectors in use today. According to the Cybersecurity and Infrastructure Security Agency (CISA), over 90% of all cyber attacks begin with phishing. Two core reasons for phishing’s prominence are: By the end of Q4 2022, the number of phishing attacks worldwide spiked to over 1.35 million. Phishing is often the first step in far more sophisticated attacks, such as: Investing in fortifying your business against phishing attacks is one of the more […]

Our newest writer, Paul Ducklin, tells it as he sees it – that we’re all served better when we treat cybersecurity as a value to be maximised, not as a cost to be minimised.


Cybersecurity is constantly evolving. As technology changes, new threats emerge, and companies are forced to find new ways to defend their organizations against those threats. Every so often, however, changes build to the point that the old way of doing things no longer works and a seismic shift is necessary. The cybersecurity industry is currently at this inflection point where something has to change. Breaches are on the rise and attackers are increasingly successful in their efforts. Cybersecurity is becoming […]




2023 has furnished an onslaught of data breaches, smashing 2022’s numbers, and putting an exclamation point on the need for companies of every size to invest in cybersecurity. By September 2023, there were already 20% more data breaches in the US than in the entirety of 2022. Probably most alarming is that 98% of all organizations have a relationship with at least one vendor that has been breached in the last two years. In an extensive study of the 2023 […]

Phishing emails are often sent out en masse and target people indiscriminately. According to a recent Gone Phishing Report, 7% of users clicked a phishing email in 2022. Of those, 44% submitted credentials in a subsequent online form. As high as these statistics are, spear phishing attacks–a highly targeted form of phishing–are much more successful. According to research by Barracuda, 11% of spear phishing email recipients click the links inside them. Let’s dive into what spear phishing is, why it’s […]

Enterprises are attractive, high-value targets for hackers; and because enterprises often have more employees and a more complicated environment, protecting against phishing and social engineering attacks is even more difficult. The Dropbox breach of late 2022 is a prime example of this weakness. Hackers emailed a large number of Dropbox employees, directing them to a malicious website where their credentials were stolen. This kind of risk is more common than not. According to the 2023 Verizon Data Breach Report, 74% […]

Business Email Compromise (BEC) is a type of email cybercrime in which attackers impersonate the owner of an email account in an effort to defraud a company. The attack, which is increasing in prevalence, often looks to obtain funds or credentials. Global losses from BEC attacks have increased by 17% from December 2021 to December 2022, reports the FBI’s Internet Crime Complaint Center (IC3). From October 2013 to December 2022, the IC3 recorded over $50 billion in global losses due […]



By subscribing you agree to our Privacy Policy and provide consent to receive updates from our company.