Script Malware: When simple things turn out hard (Part 1 of 2)
How hard can text-based malware really be? The fact that we’ve had to split this article into two parts probably gives you a hint at the answer: very hard indeed.
Phishing remains one of the most prominent attack vectors in use today. According to the Cybersecurity and Infrastructure Security Agency (CISA), over 90% of all cyber attacks begin with phishing.
Two core reasons for phishing’s prominence are:
By the end of Q4 2022, the number of phishing attacks worldwide spiked to over 1.35 million.
Phishing is often the first step in far more sophisticated attacks, such as:
Investing in fortifying your business against phishing attacks is one of the more significant steps you can take towards protecting your company. Here’s how to prevent phishing attacks in your business.
Even the most sophisticated phishing attacks typically contain one or more telltale signs. If your employees know how to spot them, you’ll dramatically reduce the risk of a successful phishing attack.
Phishing emails often contain grammatical errors either because the writer doesn’t know the language fluently or because they’re trying to get around spam filters.
Corporate emails often go through rigorous internal checks and proofreads before being approved, so it’s unlikely that a legitimate email will contain typographical or grammatical errors.
Phishing emails often contain some kind of urgency to elicit a knee-jerk response, get you to click a fraudulent link in the email, and then capture your details in a phishing website. They may pretend to be a CEO asking to send out a payment, or it might be an impersonated retailer confirming a large purchase amount.
Rule of thumb: Companies rarely send alarming emails or emails that directly ask for account details. Employees should always verify and/or reach out to IT if something looks fishy.
Although it’s possible to “spoof” a sender’s name and domain, it’s becoming more challenging as email servers crack down on reducing fraudulent emails.
As a first step, look at the sender’s domain. Phishing emails often use similar-looking domain names to evade unsuspecting victims. For example, PayPal phishing emails may use false domains such as:
…and so on.
Coupled with an urgent-sounding message and a sender name like “PayPal Customer Service,” it can be easy to miss a small detail and believe the phishing email.
Another common tactic is to use subdomains. Criminals can create a subdomain on their own fraudulent domain to improve their impersonation tactics. For example, a criminal can buy the domain customerservice123.com, allowing them to send an email from someone@paypal.customerservice123.com.
While this may seem like an easy giveaway, someone who isn’t as vigilant may see the paypal name and believe it’s a legitimate email.
Always inspect the sending domain carefully.
Industry standards such as SPF (Sender Policy Framework) and DKIM (DomainKeys Identified Mail) have greatly reduced the ability of fraudsters to forge sending addresses. Large corporations and financial institutions will typically configure SPF and DKIM capabilities for their emails, lowering the chances that fraudsters can spoof addresses from these institutions.
You can also perform manual checks to look for anomalies in a sender’s address. Tools like Google’s MessageHeader Analyzer make it easier. Just paste the “email headers” for your particular email client into the analyzer and then look at the result for anomalies such as:
The most secure approach against phishing emails is to use a combination of automated tools and thorough employee training to protect your company against phishing.
You can use filters that detect phishing emails based on the sending IP address, suspicious domains, known malicious senders, or sender reputation. These can handle most mass-phishing emails.
Most modern email clients perform SPF and DKIM checks on received emails, ensuring that the sending address hasn’t been forged. Your team should ensure that all employee email clients are up to date, and configure policies for what happens with emails that fail such checks.
Natural language processing (NLP) tools can analyze an email’s text and give it a score that will flag suspicious or illegitimate emails. You can set what happens to these emails — whether they’re blocked, or the recipient is given a warning.
For high-risk departments or addresses, such as the accounting department, you may want to adopt a stricter approach such as implementing blacklists/graylists/whitelists of domains and IP addresses. The downside with this option is that it does result in more false positives which is why it’s not ideal for the entire organization.
It’s impossible to guarantee 100% phishing prevention, so partnering with a managed security provider that understands email security and your specific business needs, goes a long way to securing your email channels and preventing successful attacks from damaging your organization too much.
Partnering with a managed security program provider can help with:
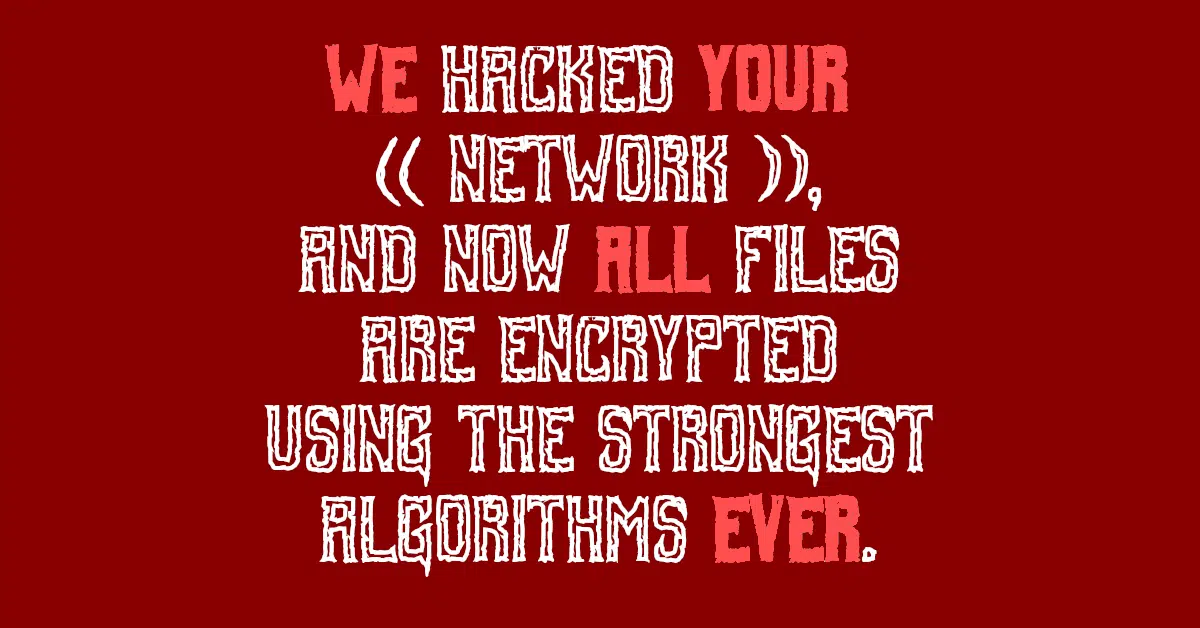
Phishing opens the door to more severe threats, such as ransomware and account compromise. A managed security program reduces the potential that your organization is susceptible to these severe threats.
SolCyber offers a foundational security package that covers the email and other security needs of most organizations. Reach out to us if you’d like to learn more about it.
How hard can text-based malware really be? The fact that we’ve had to split this article into two parts probably gives you a hint at the answer: very hard indeed.
It’s taken a while, and the suspect may never face court, but he’s been charged anyway.

Routinely review your social media privacy settings – and not just on LinkedIn.


By subscribing you agree to our Privacy Policy and provide consent to receive updates from our company.






